How I nearly took over a large games development conference
From simple information disclosure to privilege escalation, this is how poking around with one of the largest game development conferences led to revealing a critical bug.

Context
In 2024, a large games company hosted their annual conference with thousands of developers in attendance. For attendees who couldn't attend IRL, they could watch the converence via an official website - hosted by a third party events management company. This company provides services to some of the biggest in the Fortune 500.
Where did this start?
On the day of the conference, I heard from James about a vulnerability on conference's streaming site which allowed anyone to view any conference room's video feed regardless of them being live or not.
As a professional security researcher, I put my thinking cap on and replied in the most sensible way possible:
The site enforced a Referer header whitelist in order to ensure the visitor was accessing from a valid domain.
<iframe src="https://iframe.dacast.com/live/[VIDEO_ID]" style="height: 1000px; width: 1000px;"></iframe>However, this was easily bypassed by inspect-element'ing the iframe into the conference website! This led to some amazing screens being exposed...
However, this is not a major vulnerability on its own. It can't get any worse, right?
Information disclosure
During all of this, popeeyy discovered that the API for the website was leaking the IP of other attendees whilst logged in.
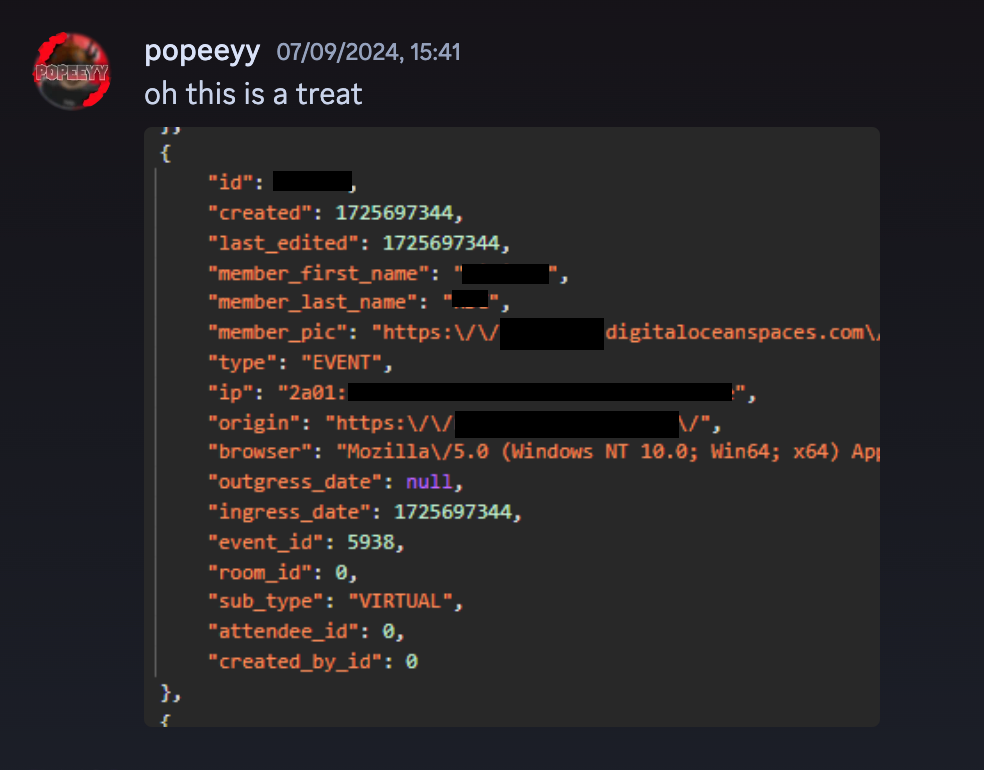
This API endpoint required you to be an attendee in order to get this information (as a non-attendee, I could only see user IDs).
Ok, so it's not as bad as I thought... righttttt? Yeah no, it still goes on.
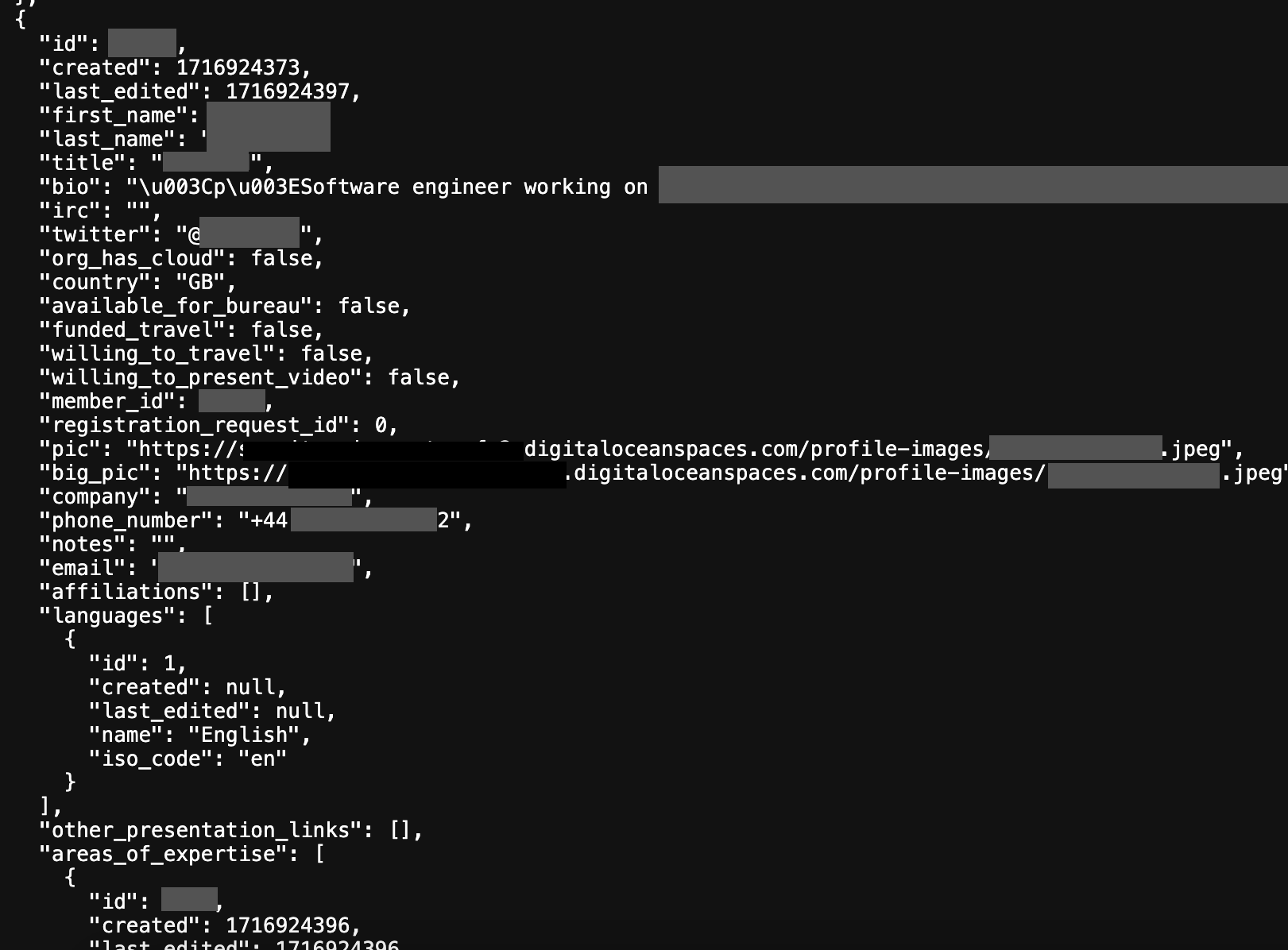
The website used DigitalOcean Spaces (S3 storage) to store the show feed, which listed all upcoming events and who was in charge of them. However, I discovered that it was storing everything about the event here - including IPs of attendees. This would allow any non-authorised user to fetch the information of attendees regardless of having an account or not.
Additionally, this CDN link was leaking the phone number of several speakers:
I bet you're wondering, how can this get any worse? Well, let me explain.
Privilege escalation
I decided to look at the conference platform's auth system, as I wanted to dig into how everything worked. Doing the usual XSS checks, username takeovers, etc and I couldn't find anything. However, I noticed how groups was being returned after updating your profile. For a standard member, this contains the item "member". At first, I tried passing admin: true and adding "admin" to the groups array, which did nothing but return an error about invalid type in the array. After that, I tried adding 1 to groups just to see what error I got. However, this happened to be the ID for the super-admins group. Did I just accidentally gave myself full admin permissions for the ENTIRE event management platform's auth system? Yes, I did...
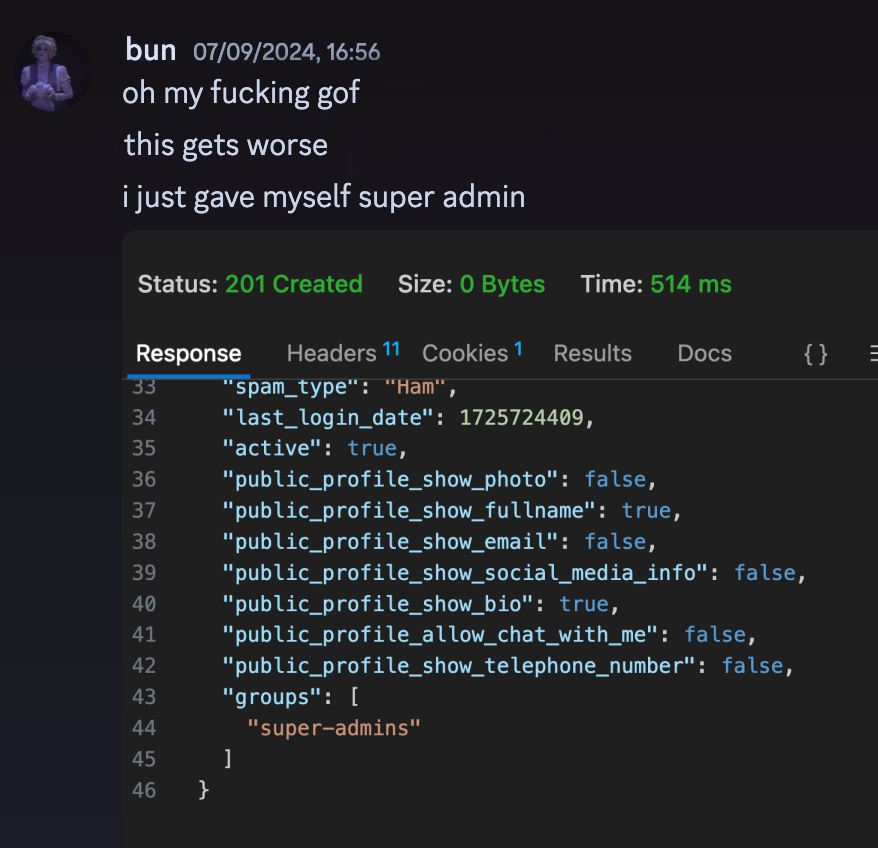
At first, I was unsure what this allowed me to do. But after refreshing the page, I saw a new item called "Server Administration" which unlocked some features not intended for the general public.
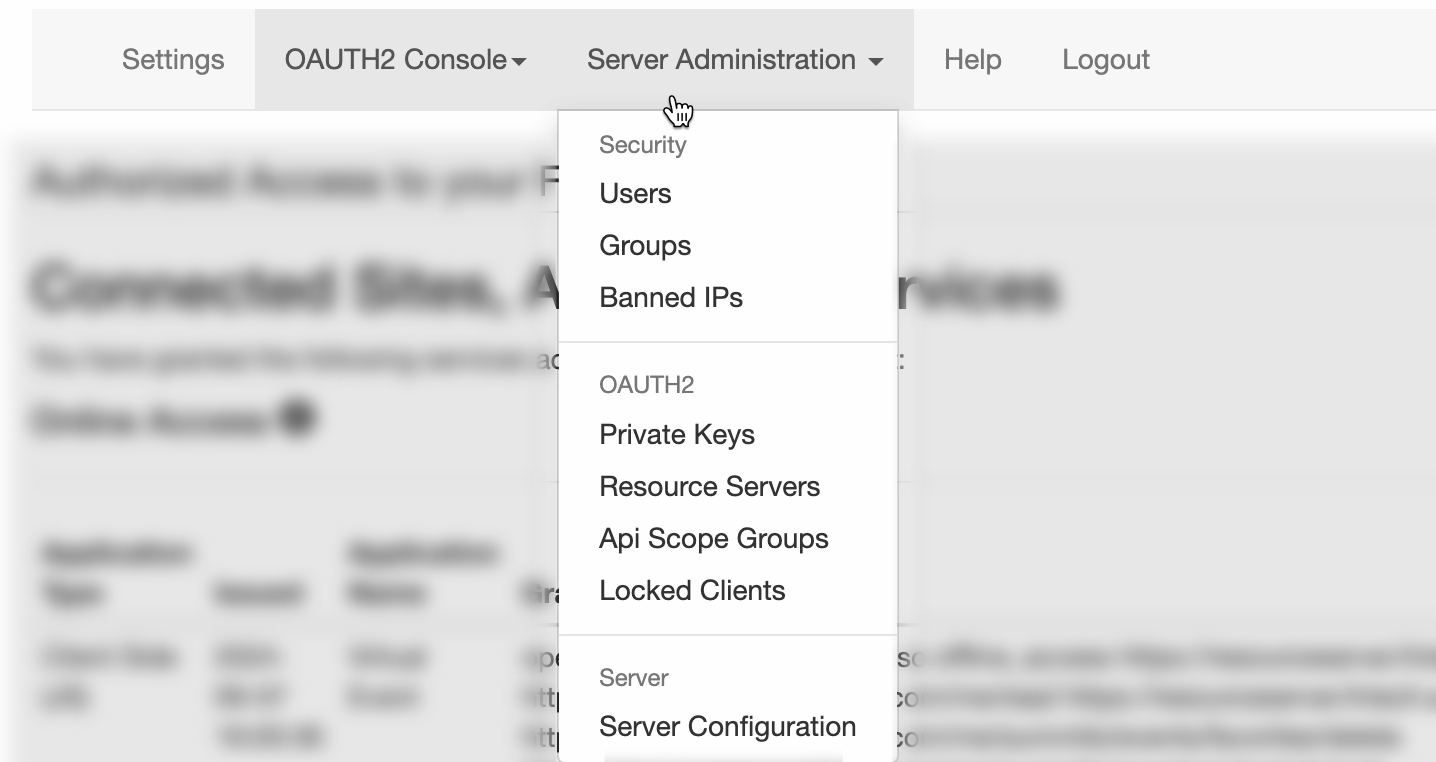
This allowed me to view the full user profile of several thousand users. Obviously, I did not store this anywhere and that information is still safe 😇. Additionally, I could view private keys for the event platform's website, see IP addresses used by different host machines (and edit them + their DNS records), and update configuration settings for all users on the site.
It's worth nothing that this wasn't just limited to the scope of the game developer conference, I had control over ANY event being hosted by this company and see PII for their users.
I also discovered that this unlocked the badge printing tool used by the events management company. This essentially gave me the option to print a badge to be able to gain access to the IRL event, which brings other security risks...
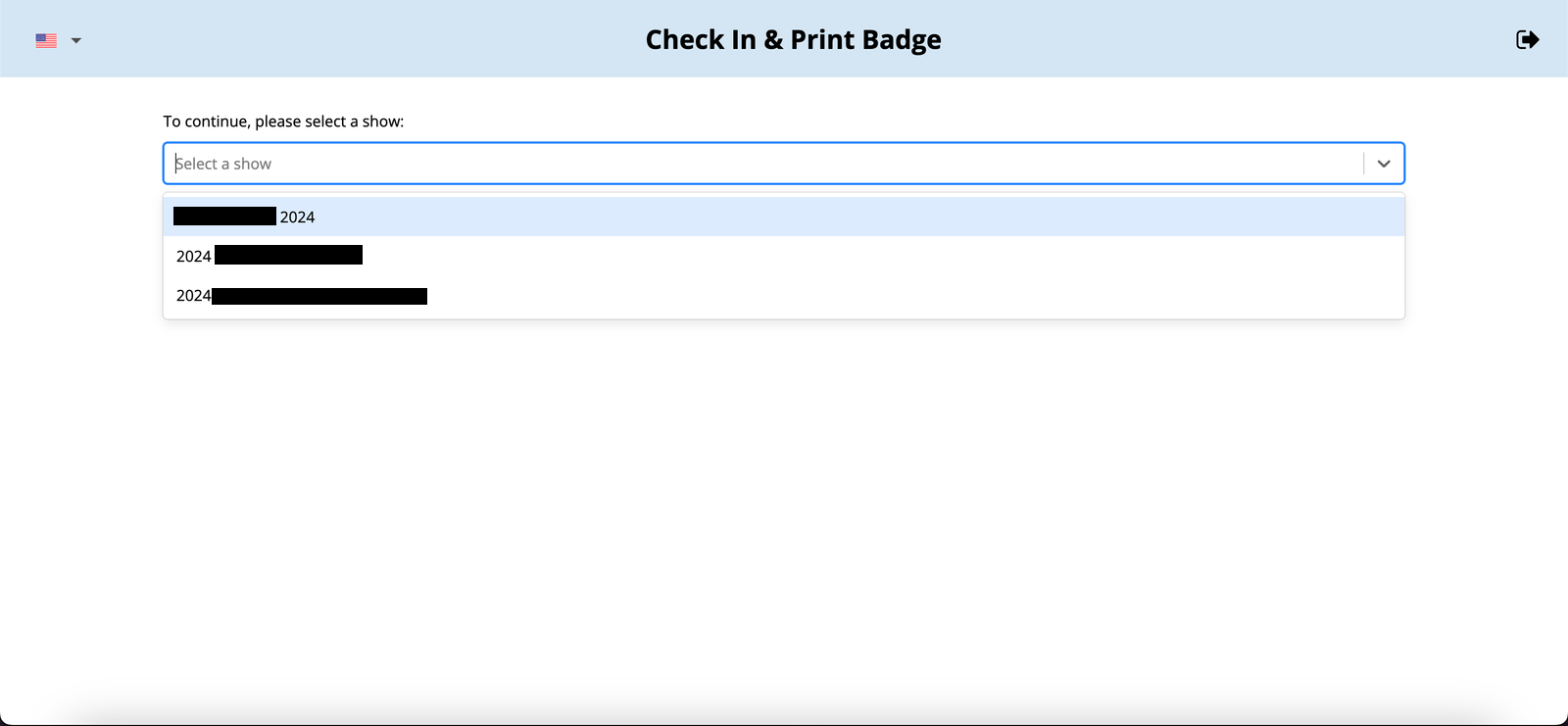
It's worth noting that this enabled me to do literally anything with the conference, including but not limited to:
- Control and replace digital sign images
- Upload and manage files
- Delete the entire event
To quickly remediate the issue, the event platform took down the conference site and purged the event from their systems (after the conference was over).
Bonus: Subdomain takeover
After this was all resolved, I did a recheck of several sites owned by the events company to see what was still possible. I saw that 2 subdomains were removed from their Netlify account and were available to takeover. I did so and alerted the company, which was subsequently handled in just over 4 hours.
Reported: 11:10PM
Resolved: 3:34AM
Conclusion
Overall, I'd say that I did not expect my weekend to go that way. Somehow, a simple test on a website led to nearly taking over an entire game development conference.
It's important to note that we immediately reported this to the appropriate people, who gave us permission to complete our testing. This really highlights the importance of bug bounty/vulnerability reporting programs - it's vital you don't overstep boundaries set by these companies as you can get yourself into a lot of trouble.
The report for this vulnerability was handed incredibly and every issue we found was resolved in real-time. The companies involved responded within 10 minutes, and we were able to get people working on patching these bugs live. I am glad action was taken before any actual abuse could take place.
Finally, I'd like to thank both James and Popeeyy - without them, the critical part of the report would not have been discovered.